Today we began or journey to Sault Ste. Marie. We start from Tobermory by hopping on the Chi-Cheemaun Ferry. The ferry ride itself accommodates mostly vehicles, such as cars, motorbikes, various recreational vehicles, vans, etc. I was impressed at how many vehicles it was able to carry in a single trip. There must have been 40 to 50 vehicles easily.
Driving into the ferry was also interesting, as there is two levels. The main level for vehicles that require extra height and motorbikes. The second level consists of mostly regular cars and SUV’s.

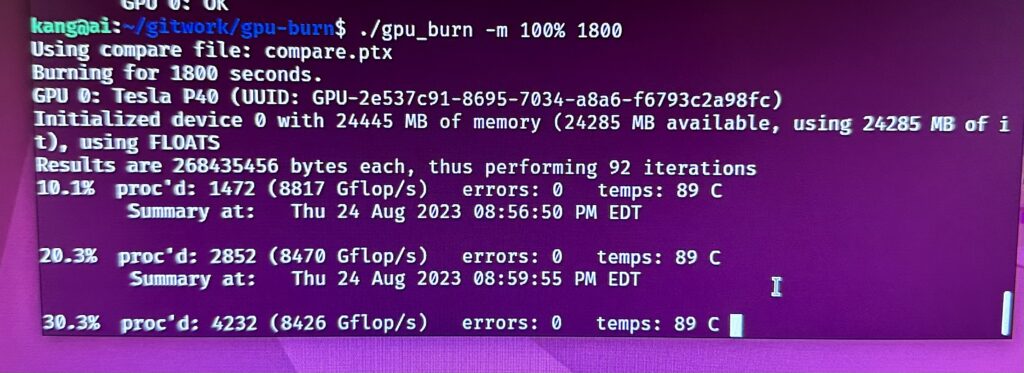
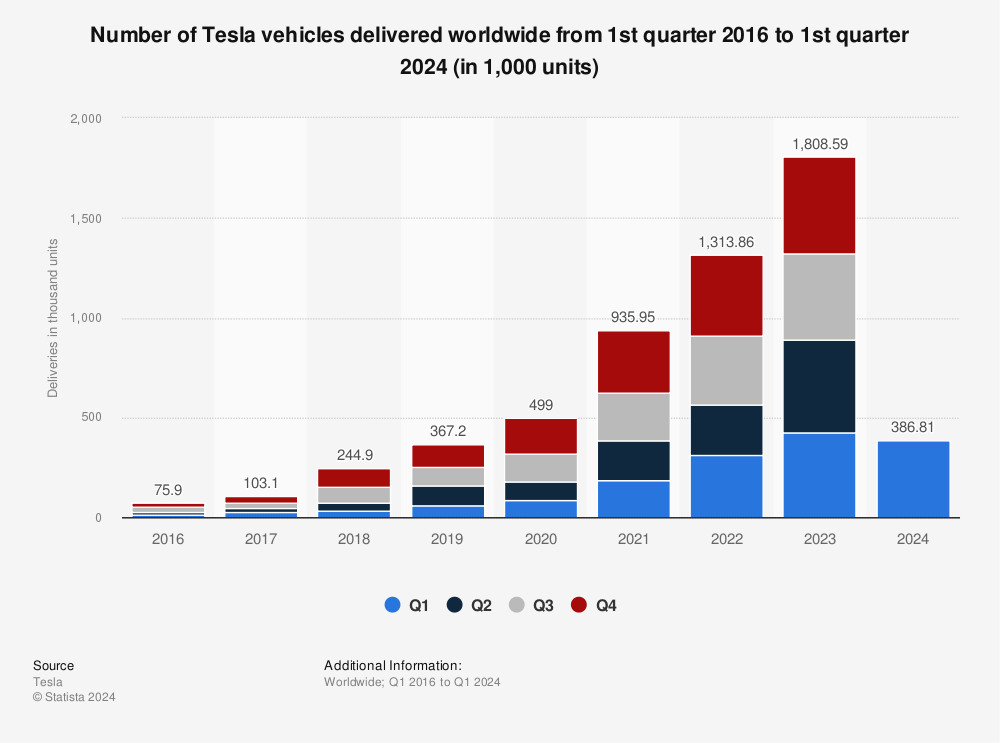
The ferry took us to South Baymouth where we had our first road trip incident with our Tesla Model Y. Because the car was transported with the ferry, it lost its GPS position and had to reacquire the signal when we get off the ferry. Well, that is how it is suppose to work. The GPS signal was acquired, but the software map on the main dash failed to update the “current position”.
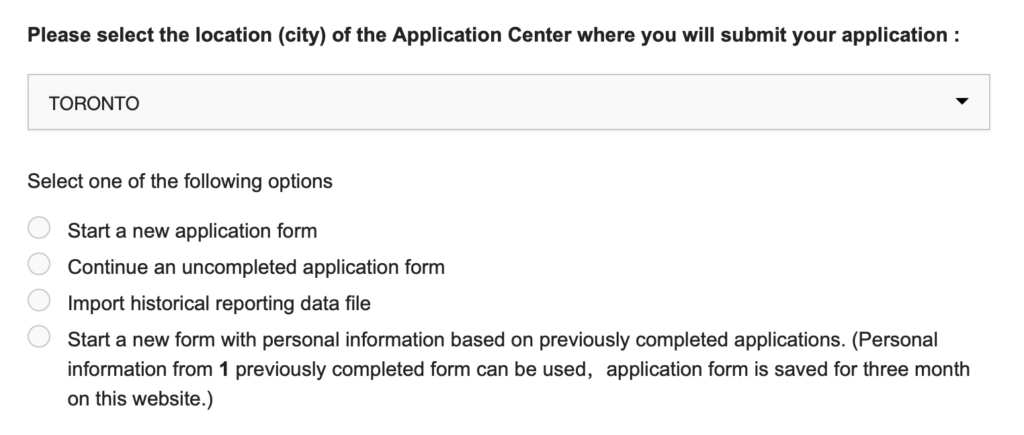
We tried the following to no avail:
- Rebooting the dash;
- Powering off and on with both a 3 minutes and 5 minutes wait;
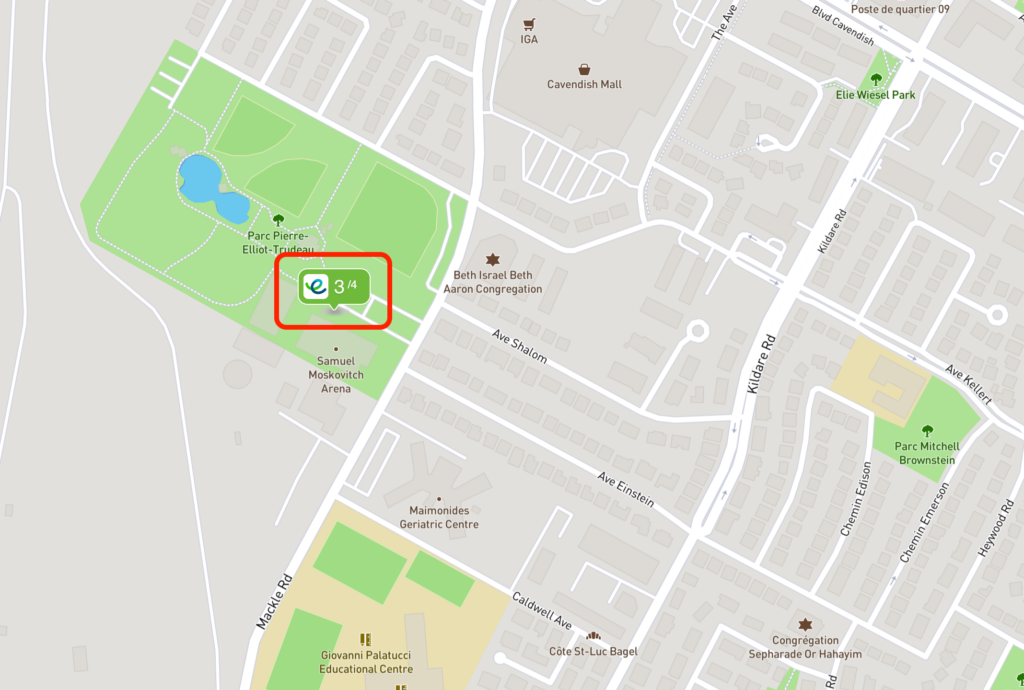
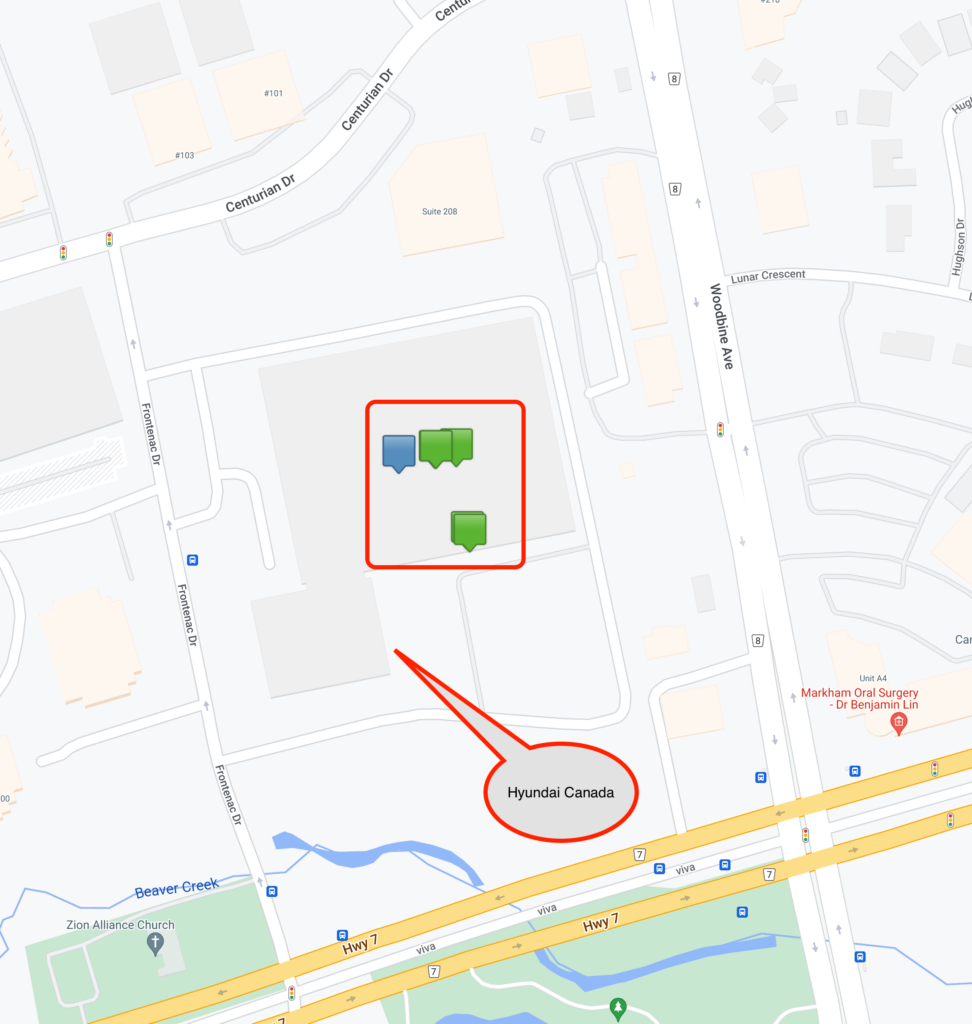
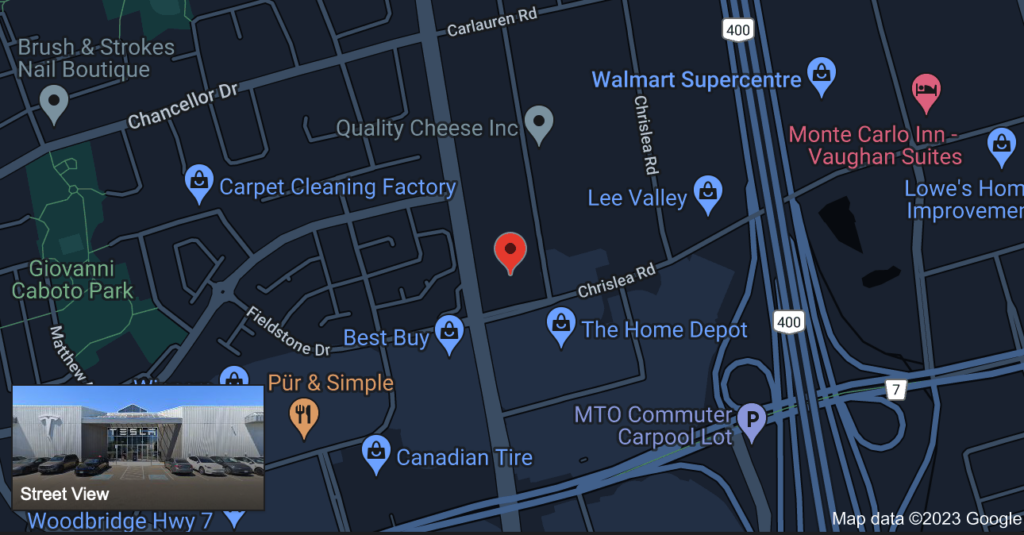
- Called Tesla support and they suggested the same with a final recommendation to drive to a Tesla Service Centre!
I am totally blown away that such a software glitch can exists on a Tesla. The fix probably just require a recycling of the GPS module. Unfortunately, there is no user-friendly way of doing this.
We gave up on our troubleshooting and drove from South Baymouth to Sault Ste. Marie without the Tesla navigation app. This is more of a handicap than I thought. The car fails to precondition the battery when we arrive at the supercharger so it takes a little longer to charge. We also miss the mapping functionality that tells us the locations of the on-route superchargers and how many were available. Good old Waze on our iPhone to the rescue, and some manual range calculations.
When we arrived at our hotel at Sault Ste. Marie, and with the help of the hotel Internet, I finally “risked” a software update on our Tesla. I had to use my iPhone’s personal hotspot and download the new software update for the Tesla. With fingers crossed and 30 minutes of unwanted and undesirable anxiety, the update downloaded successfully. Another bare knuckles 30 minutes wait, we were rewarded with a correct map and location on the dash once more!
The moral of the story is, when taking a long road trip, DO NOT transport the Tesla other than under its own power. Lesson learned! Those who are planning on taking a road trip, I highly recommend that you avoid ferries and trains that can transport your Tesla.
Tomorrow, we are off to Thunder Bay with a functional navigation system again.
Here is Carol’s video for the day.